Short Message Service Encoding Using the Rivest-Shamir-Adleman Algorithm
DOI:
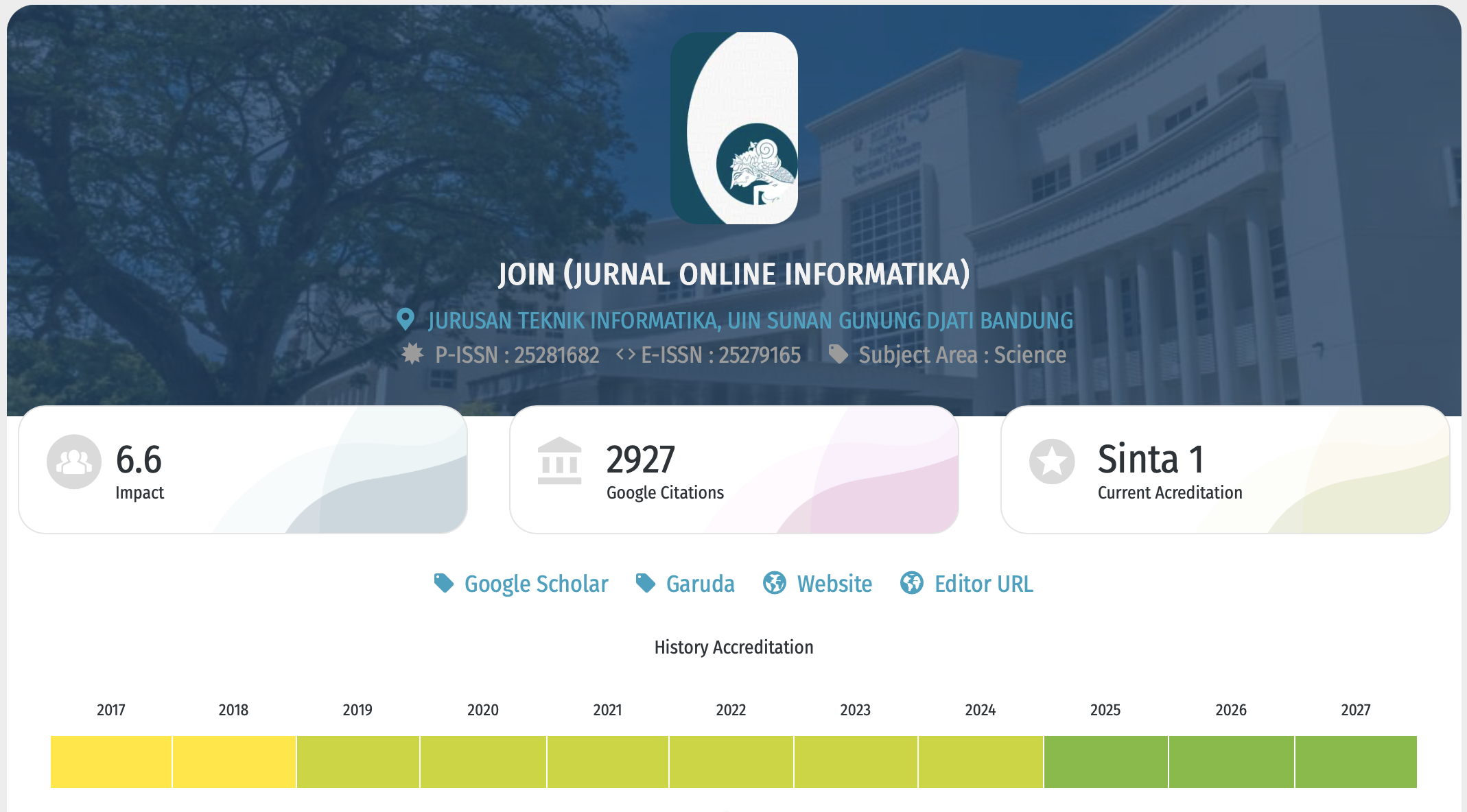
https://doi.org/10.15575/join.v4i1.264Keywords:
Android, Cryptography, Rivest-Shamir-Adleman, Short Message ServiceAbstract
SMS (Short Message Service) is one of the data exchange features in cellphones, including Android smartphones, which are the most widely used smartphone platforms today. However, the security of the SMS is questionable because the message sent must pass through a third party frist, namely SMSC (Short Message Service Center), so that message can be tapped or misused. One of the ways to reduce this risk is to encrypt or keep the original message secret by applying the cryptography algorithm. This research is to develop a system that serves to encrypt and decrypt SMS for Android-based smartphone users. The application is created to encrypt dan decrypt SMS using the Java programming language on Android, that is applied to smartphone integrated with Android Studio and used RSA cryptography algorithm. The application can be used to encrypt and decrypt SMS using the RSA algorithm on the Android-based smartphone. This application can send an SMS with a size of 86 characters and using QR Code to exchange the public key.
References
Abdiansah, “Membangun SMS-Gateway Untuk Pengisian Pulsa Elektronik,” J. Sist. Inf., vol. 1, no. 2, pp. 62–71, 2009.
A. Saputra, Membangun Aplikasi SMS dengan PHP dan MySQL. Jakarta: Elex Media Komputindo, 2011.
W. Stallings, Cryptography and Network Security: Principles and Practices, 2005.
A. J. Menezes, P. C. Van Oorschot, and S. A. Vanstone, Handbook of Applied Cryptography. Taylor & Francis Inc, 1996.
Munsyi, A. Sudarsono, and M. U. H. Al Rasyid, “Secure Data Exchange Using Authenticated Attribute-Based Encryption with Revocation for Environmental Monitoring,” Int. J. Adv. Sci. Eng. Inf. Technol., vol. 8, no. 5, p. 1948, Oct. 2018.
E. M. D. L. Reyes, A. M. Sison, and R. P. Medina, “File encryption based on reduced-round AES with revised round keys and key schedule,” Indones. J. Electr. Eng. Comput. Sci., vol. 16, no. 2, pp. 897–905, Nov. 2019.
D Ariyus, Kriptografi Keamanan Data dan Komunikasi. Yogyakarta: Graha Ilmu, 2006.
W. P. Atmojo, R. R. Isnanto, and R. Kridalukmana, “Implementasi Aplikasi Kriptografi Pada Layanan Pesan Singkat (SMS) Menggunakan Algoritma RC6 Berbasis Android,” J. Teknol. dan Sist. Komput., 2016.
P. Wicaksono, “Enkripsi Menggunakan Algoritma RSA, Makalah Ilmu Komputer,” 2013.
W. Stallings, Network and Internetwork Security Principle and Practice. Prentice Hall, 1995.
J. Katz, Introduction to Modern Cryptography, 2007.
M. Schader and A. Korthaus, The Unified Modeling Language: technical aspects and applications, 2012.
W. Ieee, “Managing the Development of Large Software Systems Dr. Winston W. Rovce Introduction,” no. August, pp. 1–9, 1970.
Hendra and Sukiman, “Aplikasi Pengaman Pertukaran SMS pada Perangkat Android dengan Metode RSA.”
B. Beizer and J. Wiley, “Black Box Testing: Techniques for Functional Testing of Software and Systems,” IEEE Softw., 2005.
Downloads
Published
Issue
Section
Citation Check
License
Copyright (c) 2019 Jurnal Online Informatika

This work is licensed under a Creative Commons Attribution-NoDerivatives 4.0 International License.
You are free to:
- Share — copy and redistribute the material in any medium or format for any purpose, even commercially.
- The licensor cannot revoke these freedoms as long as you follow the license terms.
Under the following terms:
-
Attribution — You must give appropriate credit, provide a link to the license, and indicate if changes were made. You may do so in any reasonable manner, but not in any way that suggests the licensor endorses you or your use.
-
NoDerivatives — If you remix, transform, or build upon the material, you may not distribute the modified material.
-
No additional restrictions — You may not apply legal terms or technological measures that legally restrict others from doing anything the license permits.
Notices:
- You do not have to comply with the license for elements of the material in the public domain or where your use is permitted by an applicable exception or limitation.
- No warranties are given. The license may not give you all of the permissions necessary for your intended use. For example, other rights such as publicity, privacy, or moral rights may limit how you use the material.

This work is licensed under a Creative Commons Attribution-NoDerivatives 4.0 International License