Optimizing Hypertension Prediction from Electronic Health Records via Hybrid ANN–LSTM with Ant Colony and Bayesian Optimization
DOI:
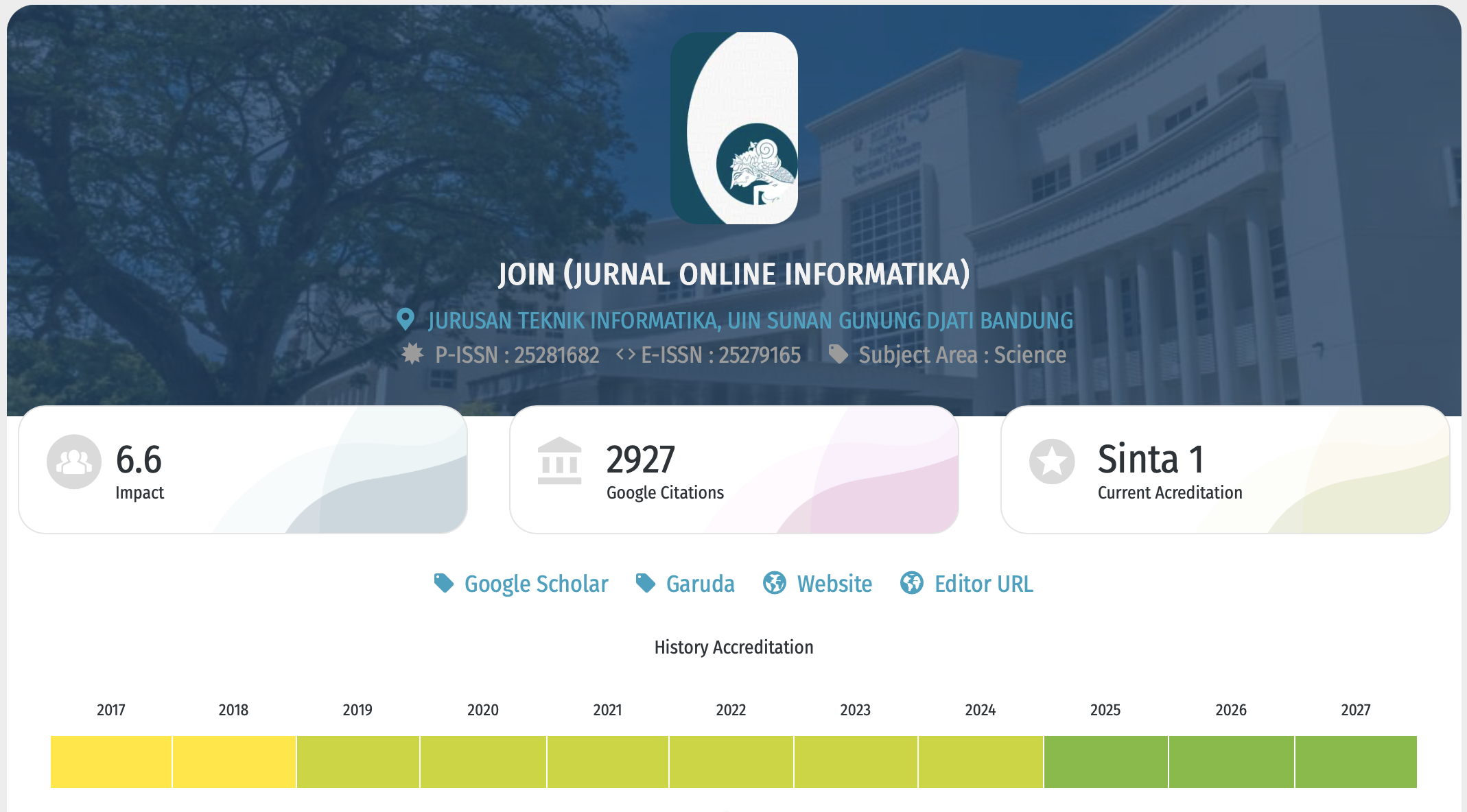
https://doi.org/10.15575/join.v11i1.1723Keywords:
Ant Colony Optimization, Bayesian Optimization, Electronic Health Records, Hybrid Deep Learning, Hypertension Prediction, SMOTEAbstract
References
[1] C. Elendu, D. C. Amaechi, T. C. Elendu, E. C. Amaechi, and I. D. Elendu, “Dependable approaches to hypertension management: A review.,” Medicine, vol. 103, no. 24, p. e38560, Jun. 2024, doi: 10.1097/MD.0000000000038560.
[2] C. Abbafati et al., “Global burden of 369 diseases and injuries in 204 countries and territories, 1990–2019: a systematic analysis for the Global Burden of Disease Study 2019,” The Lancet, vol. 396, no. 10258, pp. 1204–1222, 2020, doi: 10.1016/S0140-6736(20)30925-9.
[3] P. Verdecchia, J. A. Staessen, W. B. White, Y. Imai, and E. T. O’Brien, “Properly defining white coat hypertension,” Eur. Heart J., vol. 23, no. 2, pp. 106–109, 2002, doi: 10.1053/euhj.2001.2657.
[4] L. S. Chow et al., “Time-Restricted Eating Effects on Body Composition and Metabolic Measures in Humans who are Overweight: A Feasibility Study,” Obesity, vol. 28, no. 5, pp. 860–869, 2020, doi: 10.1002/oby.22756.
[5] A. Esteva et al., “Dermatologist-level classification of skin cancer with deep neural networks,” Nature, vol. 542, no. 7639, pp. 115–118, 2017, doi: 10.1038/nature21056.
[6] A. C. Ian Goodfellow, Yoshua Bengio, “Deep Learning,” MIT Press, vol. 521, no. 7553, p. 785, 2017, doi: 10.1016/B978-0-12-391420-0.09987-X.
[7] M. K. Khalifaturohman, “Systematic Literature Review: Deep Learning Models in Arabic Script Classification,” Khazanah Journal of Religion and Technology, vol. 3, no. 1, pp. 18–22, Jul. 2025, doi: 10.15575/kjrt.v3i1.1619.
[8] A. Rajkomar et al., “Scalable and accurate deep learning with electronic health records,” NPJ Digit. Med., vol. 1, no. 1, pp. 1–10, 2018, doi: 10.1038/s41746-018-0029-1.
[9] M. Dorigo and T. Stützle, Handbook of Metaheuristics; Ant colony optimization: Overview and recent advances, vol. 272. 2019.
[10] J. Snoek, H. Larochelle, and R. P. Adams, “Practical Bayesian optimization of machine learning algorithms,” Adv. Neural Inf. Process. Syst., vol. 4, pp. 2951–2959, 2012.
[11] R. Vargas, A. Mosavi, R. Ruiz, and S. Engineering, “DEEP LEARNING : A REVIEW,” no. October, 2018, doi: 10.20944/preprints201810.0218.v1.
[12] Muhammad Haris Diponegoro, Sri Suning Kusumawardani, and Indriana Hidayah, “Tinjauan Pustaka Sistematis: Implementasi Metode Deep Learning pada Prediksi Kinerja Murid,” Jurnal Nasional Teknik Elektro dan Teknologi Informasi, vol. 10, no. 2, pp. 131–138, 2021, doi: 10.22146/jnteti.v10i2.1417.
[13] Asniar, N. U. Maulidevi, and K. Surendro, “SMOTE-LOF for noise identification in imbalanced data classification,” Journal of King Saud University - Computer and Information Sciences, vol. 34, no. 6, pp. 3413–3423, 2022, doi: 10.1016/j.jksuci.2021.01.014.
[14] Y. Lecun, Y. Bengio, and G. Hinton, “Deep learning,” Nature, vol. 521, no. 7553, pp. 436–444, 2015, doi: 10.1038/nature14539.
[15] K. Greff, R. K. Srivastava, J. Koutník, B. R. Steunebrink, and J. Schmidhuber, “TRANSACTIONS ON NEURAL NETWORKS AND LEARNING SYSTEMS 1 LSTM: A Search Space Odyssey,” arXiv:1503.04069, pp. 1–11, 2015.
[16] M. Mohamed, A. Abdullah, A. M. Zaki, F. H. Rizk, M. M. Eid, and E. M. El El-Kenway, “Advances and Challenges in Feature Selection Methods: A Comprehensive Review,” Journal of Artificial Intelligence and Metaheuristics, vol. 7, no. 1, pp. 67–77, 2024, doi: 10.54216/jaim.070105.
[17] A. Jović, K. Brkić, and N. Bogunović, “A review of feature selection methods with applications,” 2015 38th International Convention on Information and Communication Technology, Electronics and Microelectronics, MIPRO 2015 - Proceedings, no. May 2015, pp. 1200–1205, 2015, doi: 10.1109/MIPRO.2015.7160458.
[18] B. Z. Dadaneh, H. Y. Markid, and A. Zakerolhosseini, “Unsupervised probabilistic feature selection using ant colony optimization,” Expert Syst. Appl., vol. 53, pp. 27–42, 2016, doi: 10.1016/j.eswa.2016.01.021.
[19] E. E. Putri, B. S. Hasugian, A. Info, and D. Mining, “Pattern Analysis of Drug Procurement System With FP-Growth Algorithm,” vol. 7, no. 1, pp. 70–79, 2022, doi: 10.15575/join.v7i1.841.
[20] B. Shahriari, K. Swersky, Z. Wang, R. P. Adams, and N. De Freitas, “Taking the human out of the loop: A review of Bayesian optimization,” Proceedings of the IEEE, vol. 104, no. 1, pp. 148–175, 2016, doi: 10.1109/JPROC.2015.2494218.
[21] J. Cheng and M. Lapata, “Neural summarization by extracting sentences and words,” 54th Annual Meeting of the Association for Computational Linguistics, ACL 2016 - Long Papers, vol. 1, pp. 484–494, 2016, doi: 10.18653/v1/p16-1046.
[22] S. Li, J. Wang, and P. Liu, “Detection of Generative Linguistic Steganography Based on Explicit and Latent Text Word Relation Mining Using Deep Learning,” IEEE Trans. Dependable Secure Comput., vol. 20, no. 2, pp. 1476–1487, 2023, doi: 10.1109/TDSC.2022.3156972.
[23] Y. Deng, M. R. Eden, and S. Cremaschi, “Metrics for Evaluating Machine Learning Models Prediction Accuracy and Uncertainty,” in 33rd European Symposium on Computer Aided Process Engineering, vol. 52, A. C. Kokossis, M. C. Georgiadis, and E. Pistikopoulos, Eds., in Computer Aided Chemical Engineering, vol. 52. , Elsevier, 2023, pp. 1325–1330. doi: https://doi.org/10.1016/B978-0-443-15274-0.50211-0.
[24] R. Fayzrakhmanov, A. Kulikov, and P. Repp, “The difference between precision-recall and ROC curves for evaluating the performance of credit card fraud detection models,” Proceedings of International Conference on Applied Innovation in IT, vol. 6, no. 1, pp. 17–22, 2018.
[25] B. Ambu-Saidi, Fung, C.Y., Turner, K., and Lim, A.S.S., “A Critical Review on Training Evaluation Models: A Search for Future Agenda,” Journal of Cognitive Sciences and Human Development, vol. 10, no. 1, pp. 142–170, 2024, doi: 10.33736/jcshd.6336.2024.
Downloads
Published
Issue
Section
Citation Check
License
Copyright (c) 2026 Zulham, Junadhi

This work is licensed under a Creative Commons Attribution-NoDerivatives 4.0 International License.
You are free to:
- Share — copy and redistribute the material in any medium or format for any purpose, even commercially.
- The licensor cannot revoke these freedoms as long as you follow the license terms.
Under the following terms:
-
Attribution — You must give appropriate credit, provide a link to the license, and indicate if changes were made. You may do so in any reasonable manner, but not in any way that suggests the licensor endorses you or your use.
-
NoDerivatives — If you remix, transform, or build upon the material, you may not distribute the modified material.
-
No additional restrictions — You may not apply legal terms or technological measures that legally restrict others from doing anything the license permits.
Notices:
- You do not have to comply with the license for elements of the material in the public domain or where your use is permitted by an applicable exception or limitation.
- No warranties are given. The license may not give you all of the permissions necessary for your intended use. For example, other rights such as publicity, privacy, or moral rights may limit how you use the material.

This work is licensed under a Creative Commons Attribution-NoDerivatives 4.0 International License